Table of contents
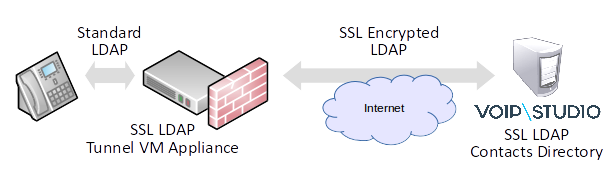
Cisco SPAxxx phones allow for central LDAP server to act as an contacts directory. It is a great way to centrally manage telephone numbers employees need to have an easy access on their desk phones. Unfortunately Cisco SPAxxx phones only allow connection to a standard (ie. not SSL enabled) LDAP server. This may pose a problem in environments where data privacy and security is of paramount importance. To overcome this limitation of Cisco phones a LDAP SSL Tunnel virtual appliance may be deployed on the same local network where the phones are. This way phones will communicate over local LAN with the appliance and further communication over public Internet is secured with strong SSL encryption.
The process of creating secure SSL LDAP tunnel involves two major steps:
1. Deploying VM LDAP SSL Tunnel appliance. In this tutorial we will use VMWare EXSi 5.5, however since the appliance is provided in OVF (Open Visualization Format) any hypervisor supporting this standard can be used.
2. Creating custom Cisco Provisioning Template to make phones use local IP LAN IP address (assigned to VM LDAP SSL Tunnel appliance) as LDAP server.
Deploy LDAP SSL Tunnel appliance
To deploy and configure the appliance follow steps show below.
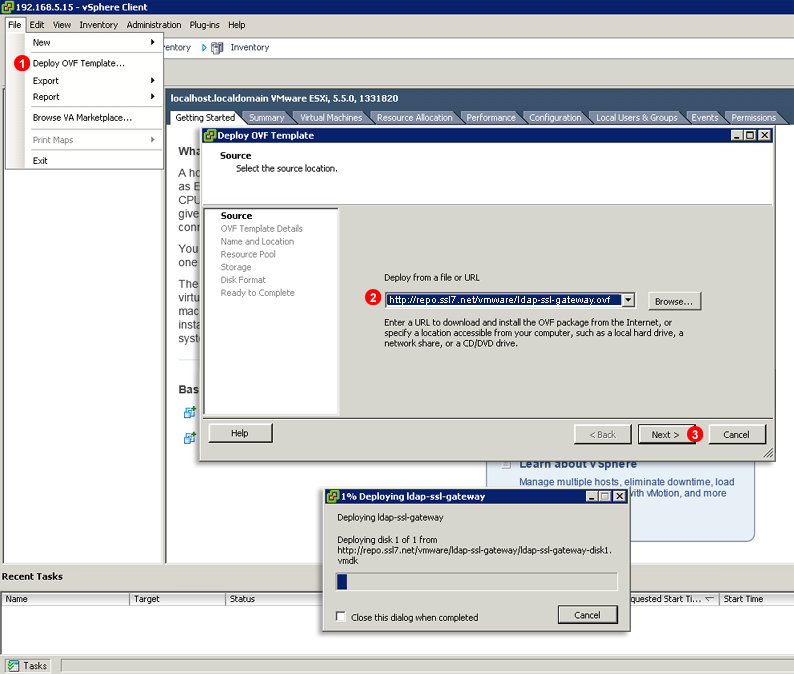
Deploy OVF image
1. Start VMWare ESXi client and select Deploy OVF Template… from File menu.
2. Enter http://repo.ssl7.net/vmware/ldap-ssl-gateway.ovf into Deploy from file or URL field.
3. Click Next > and follow OVF deployment wizard.
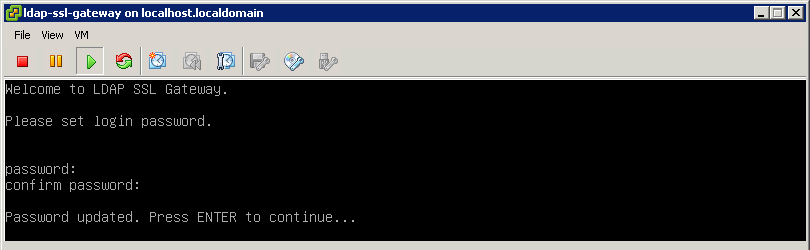
Set VM appliance login password
Once OVF image is deployed start the Virtual Machine. When it boots you will be asked to set the login password. It has to be minimum 6 characters long. The username to login into the appliance is: ldaps
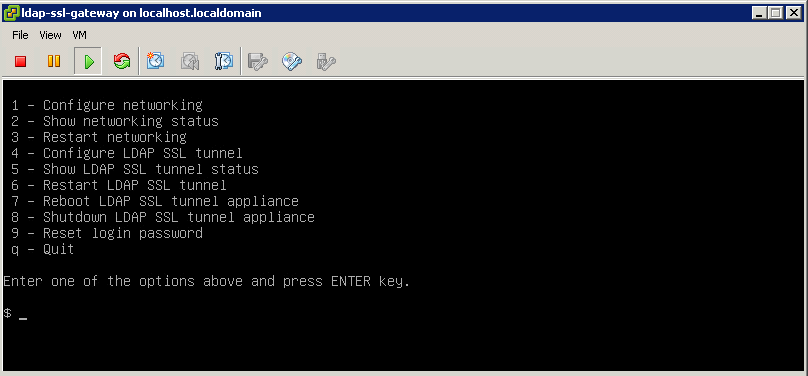
VM appliance main menu
When the login password is set you will be presented with the main menu. We will use it in steps below to configure networking and verify secure LDAP SSL tunnel is working correctly.
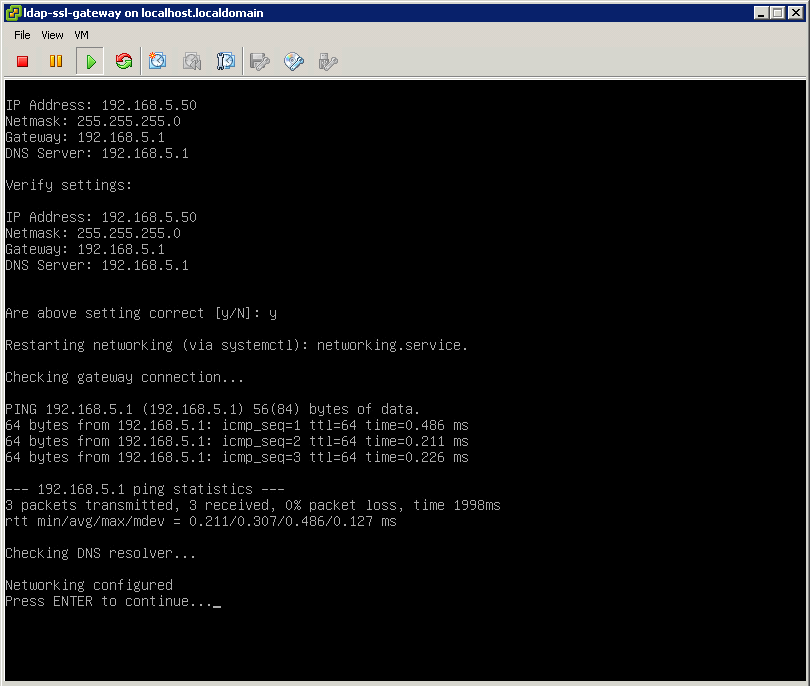
VM appliance networking configuration
Press 1 to enter Networking Configuration screen. Here you will be prompted for IP address, netmask, default gateway and DNS server address. Since the appliance IP address will be entered into phone’s provisioning template it cannot use DHCP server to obtain random IP address. Rather it has to be using static IP address. Once networking configuration is correct press Enter key to go back to the main menu.
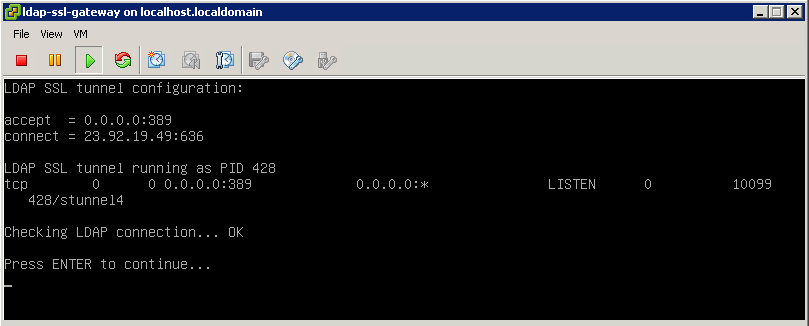
VM appliance LDAP SSL tunnel test
The appliance is pre-configured with VoIPstudio LDAP server IP address, so there is no need to perform and LDAP tunnel configuration. We can proceed to testing if SSL tunnel is working correctly. Press 5 to enter LDAP status page. After a short while you should see a screen similar to the above image.
Custom Provisioning Template
Once we have VM appliance configured we can proceed to creating customer Cisco Provisioning Template to make the phones use IP address of the VM appliance for LDAP directory searches.
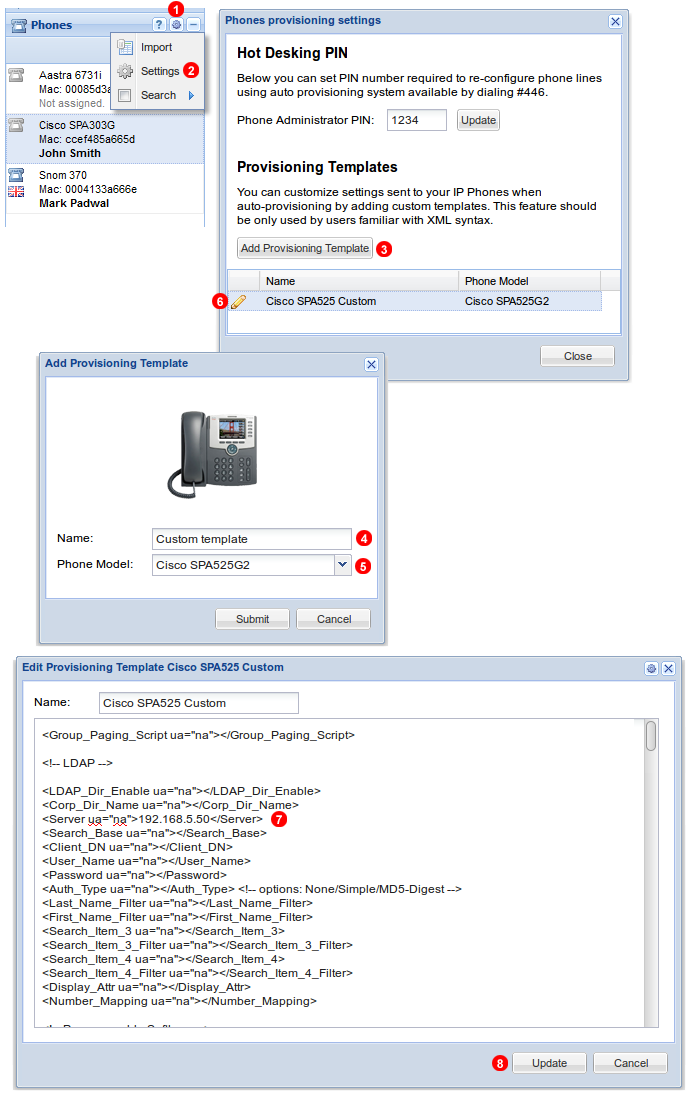
Add custom provisioning template
Follow steps below to create custom provisioning template for Cisco phone:
- Click gear icon in top left part of Phones panel.
- Select Settings from the menu.
- Click Add Provisioning Template button.
- Enter template name.
- Select phone make and model.
- Click pencil icon to edit template.
- Enter IP address of your VM appliance into
<Server ua="na">192.168.5.50</Server>tag (note: address 192.168.5.50 is just an example, you will need to enter your own IP address here). - Click Update button to save changes.
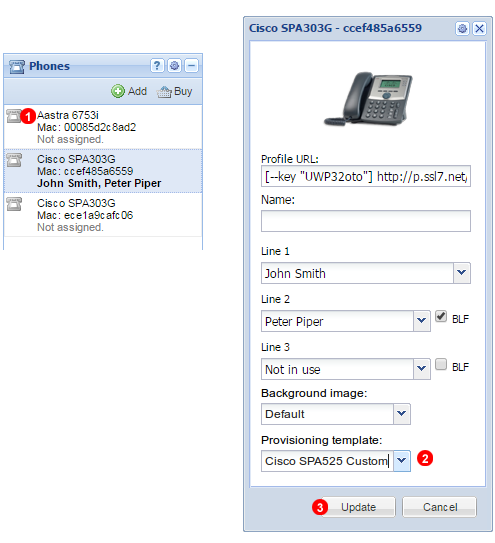
Assign custom provisioning template to the phone
Finally we can assign our custom template to the phones to make them start using VM appliance for LDAP queries:
- Click icon next to the phone you want to edit.
- Use Provisioning template drop down to select custom template.
- Click Update button. After a short while the phone will reboot and new configuration will be uploaded.
More from the blog
Want to improve your business communication?
Unlock enterprise-class call center power at affordable prices – no hardware, no delays, no surprises!